This blog article explains the key features in VMware's App Volumes, an app packaging solution with Apps on Demand real-time delivery and management. Find out how to streamline your application delivery with App Volumes and Apps on Demand in this…

AI/ML's opaque processes challenge data quality and decision-making, emphasizing the need for understanding and control. Read More...

Secure-by-design—a CISA philosophy encouraging software manufacturers to design products in a way that minimizes security vulnerabilities—requires deft implementation. Here's the breakdown: Read More...

Separately, Wi-Fi and 5G are amazing technologies. When used together, they are unleashing incredible capabilities for enterprises, as in 1+1=3. Read More...
Cloud Security Compliance Desktop Security MTR Rapid Response Best Results As of December 2023, small and mid-sized businesses are facing a range of cybersecurity threats that have evolved in complexity and impact. These include ransomware attacks, vulnerabilities in hybrid data…
RUDN University economist and colleagues analyzed data from the largest oil and gas companies in Russia during the economic crises of 2020 and 2022 and proposed an algorithm that would increase the sustainability of the industry. The key factor here…
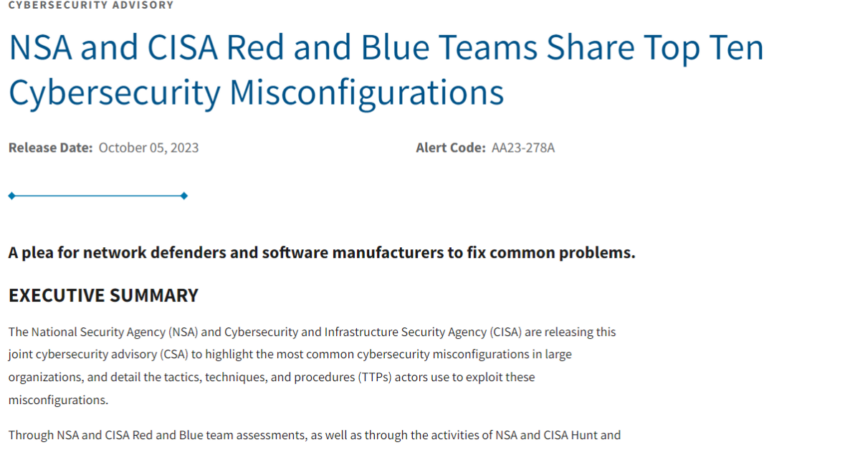
According to NSA and CISA, the worst cybersecurity misconfigurations include insufficient internal network monitoring, lack of network segmentation, and poor patch management. See the full list: Read More...

Here you'll find a complete list of all the known layoffs in tech, from Big Tech to startups, broken down by month throughout 2023. Read More...

If you've come across countless examples of how AI is transforming businesses and even entire industries, but aren't sure how to best implement this novel tech inside your organization, schedule a complimentary demo with one of our AI experts to…

Which new cyberattack vectors and tactics pose the biggest risk to your networks, data and hardware? Schedule a free consultation with one of our experts for a comprehensive overview of today's most dangerous threats. View: Secure your organization against new…
